Difference between revisions of "Math Modeling Pages"
KrMuscalino (talk | contribs) (→Hash Functions) |
KrMuscalino (talk | contribs) (→Website of Our Hash Functions) |
||
| (5 intermediate revisions by the same user not shown) | |||
| Line 88: | Line 88: | ||
==Hash Function Characteristics== | ==Hash Function Characteristics== | ||
| + | |||
| + | |||
| + | [[Image:corlat.jpg]] | ||
| + | |||
| + | [[Image:corlate2.jpg]] | ||
| + | |||
| + | == Website of Our Hash Functions == | ||
| + | |||
| + | *[http://gcat.davidson.edu/StudentProjects/womp/hashhome.html Biological Hashing Website] | ||
== Models == | == Models == | ||
| Line 120: | Line 129: | ||
==[[Matlab M-files for Math Models]]== | ==[[Matlab M-files for Math Models]]== | ||
| + | |||
| + | ==Analysis== | ||
| + | |||
| + | [[Image:Slide1.jpg]] | ||
| + | |||
| + | ==Results== | ||
== Papers == | == Papers == | ||
Latest revision as of 21:16, 25 July 2008
This is the place for math modelers to post ideas, papers, examples and computer programs.
Contents
- 1 Created Kinetic Law for Double Promoter
- 2 Km Values for Models
- 3 SimBio Update, July 9, 2008
- 4 SimBiology (from MATLAB)
- 5 Hash Function Characteristics
- 6 Website of Our Hash Functions
- 7 Models
- 8 Matlab M-files for Math Models
- 9 Analysis
- 10 Results
- 11 Papers
- 12 Logical negation
- 13 Logical conjunction
- 14 Exclusive disjunction
- 15 Logical NAND
- 16 Logical NOR
- 17 Engineering agar
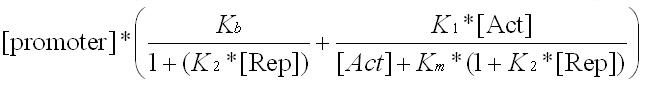
Created Kinetic Law for Double Promoter
As of 7/3/08
Link to ETH Zurich 2007 iGEM page for constants
http://parts.mit.edu/igem07/index.php/ETHZ/Engineering
The following units should be used (we think) for the expression above which gives the level of transcription for any doubly-regulated promoter. Pay close attention to the units of molecules as it is critical that we have molecules of the correct schtuff.
[pro] is in molecules of promoter
[rep] is in molecules of repressor
[act] is in molecules of activator
K b is in molecules of mRNA per (second * molecules of promoter) which makes sense for the basal rate (Yea!!)
K 1 is the same units as K b
K 2 is in 1/molecules of repressor (making the first denominator unitless)
K m is in molecules of activator (so that addition in denominator of second fraction is well-defined)
Note that the units of the overall product are molecules of mRNA per second, as needed. Note also that we want K 2 in the denominator of the first fraction to have the units described above and substituting (K 2 ) 2 as discussed durring "MWSU to Davidson" week would mess up the units on K b which would lead to serious problems with the model. If we need different numbers numerically in the two terms, we will need to go to K 3 as a separate constant but preserve the units by making K 3 have the same units as K 2 .
Km Values for Models
LIST OF Km Values
- Km of 3OC12 for LasR is 1 nM (Egland and Greenberg, 2000)
- Km of 3OC6 for LuxR is 100 nM (Urbanowski et al., 2004)
- Km of LasR* for operator/promoter is 11 pM (Schuster et al, 2004)
- Km of LuxR* for operator/promoter is 10 nM (Kaplan and Greenberg, 1987)
- Km of cI dimer for OR1 and OR2 is 10 pM (King et al., 1993)
- Km of Mnt tetramer for binding to half operator/promoter is 50 nM and binding whole operator is 1 nM (Berggrun and Sauer, 2001)
- Km of Lsr for its binding site is X nM (no data available)
- Km of AI-2 for LsrR is X nM (no data available)
- Km of IPTG for LacI is 1.3 µM (Gilbert and Muller-Hill, 1966)
- Km of LacI for its binding site is 10 pM (Gilbert and Muller-Hill, 1967)
- Km of LacI-I12 for its binding site is 0.13 pM (calculated from Schmitz and Galas, 1980; and Schmitz et al., 1978)
- Km of LacI-X86 for its binding site is 0.13 pM (calculated from Schmitz and Galas, 1980; and Schmitz et al., 1978)
- Km of LacI-I12_X86 for its binding site is 0.001 pM (calculated from Schmitz and Galas, 1980; and Schmitz et al., 1978)
- Half life of molecules in E. coli: 2 minutes for mRNA; 1 molecule is 1 nM concentration (Fang Ph.D. Thesis, 2007); translation rate 15 amino acids per second and transcription is 40 nt per second (from Genes VII by Lewin).
SimBio Update, July 9, 2008
Our new model has been condensed to 10 reactions. Reactions (1) and (9) have been condensed to reaction (5), while Reactions (2) and (10) have been condensed to reaction (6).
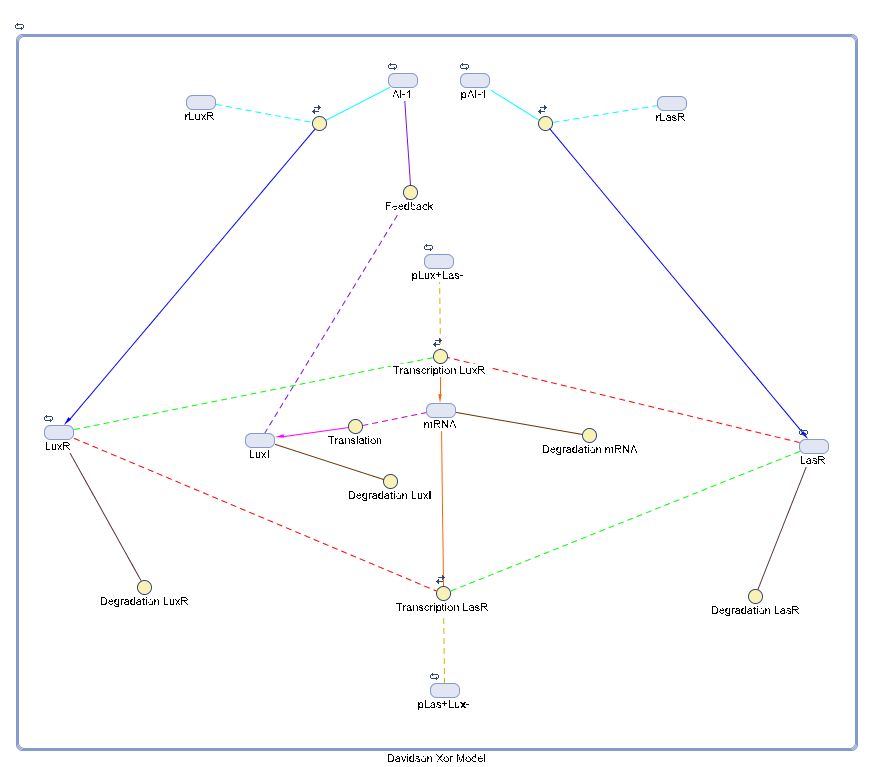
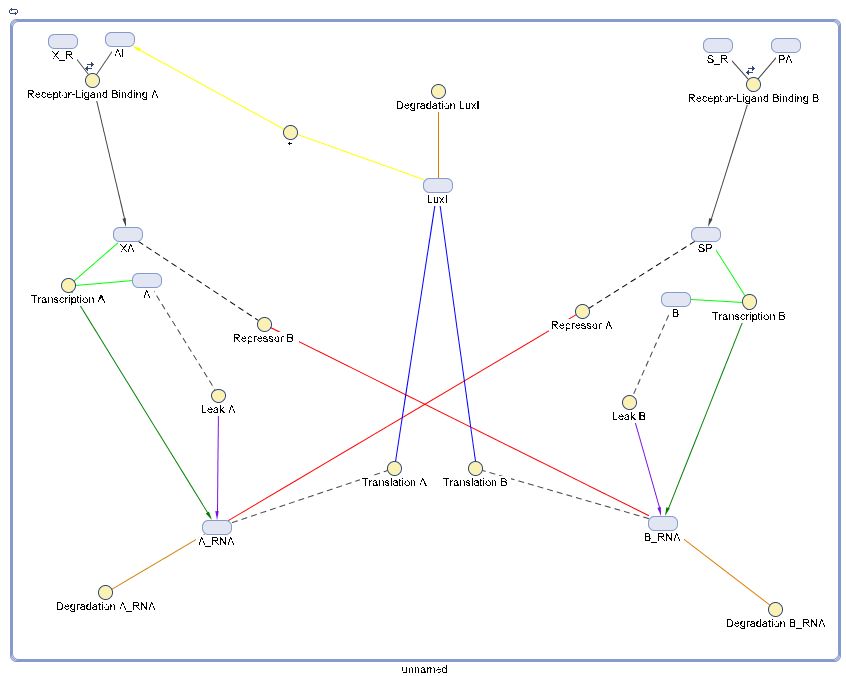
SimBiology (from MATLAB)
We are attempting to create an accurate model of all the biological processes which will be
present in the XOR gate when it is activated. Listed are some of the possible reactions we have
come up with thus far, along with a short explanation of each of the reactions' respective
functions.
(1) A -> A_RNA + A (Leak, Transcription) - Before the model is activated, we must account for a small portion of Transcription to naturally occur.
(2) B -> B-RNA + B - Same as (1)
(3) X_R + AI <-> XA (Receptor-Ligand Binding) - This is where LuxR and AI-1 bind to create the protein.
(4) S_R + PA <-> SP - Where LasR and pAI-1 bind
(5) XA + A -> A_RNA (Transcription) - The LuxR-AI-1 protein encodes into the pLux + Las- DNA and transcribes into the mRNA.
(6) SP + B -> B_RNA - The LasR-pAI-1 encodes into the pLas + Lux- DNA and transcribes into the mRNA
(7) A_RNA -> A_RNA + LuxI (Translation) - The mRNA is translated into the desired protein, LuxI.
(8) B_RNA -> B_RNA + LuxI - Same as (7)
(9) SP + A_RNA -> SP (Repressor) - The LasR-pAI-1 protein encodes onto the pLux + Las- DNA and represses the LuxR-AI-1 protein, inhibiting transcription of the mRNA.
(10) XA + B_RNA -> XA - The LuxR-AI-1 protein encodes onto pLas + Lux- DNA and represses the LasR-pAI-1 protein, inhibiting transcription of the mRNA.
(11) A_RNA -> null (Degradation) - After being translated, it will eventually degrade.
(12) B_RNA -> null - Same as (11)
(13) LuxI -> null - Same as (11)
(14) LuxI -> AI (*) - Protein LuxI is known to bind with AI-1.
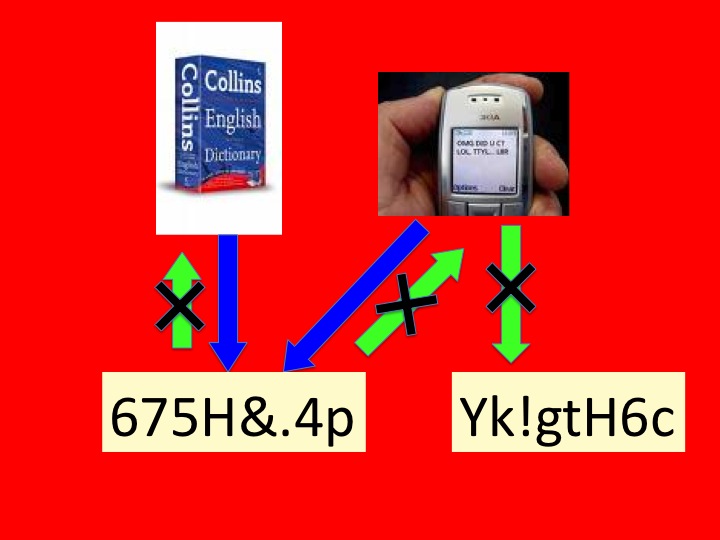
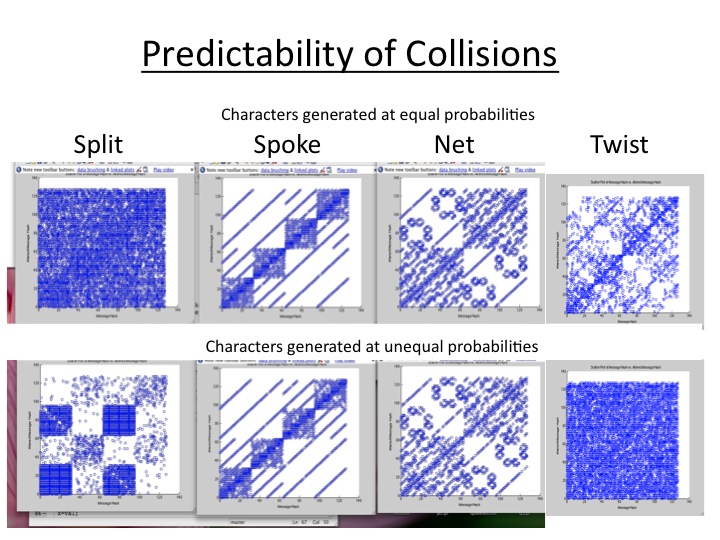
Hash Function Characteristics
Website of Our Hash Functions
Models
Davidson Hash Function Models
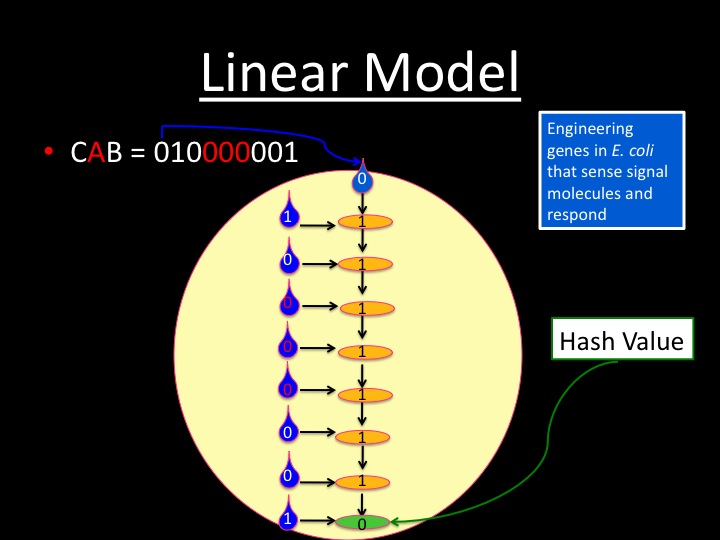
Linear Model
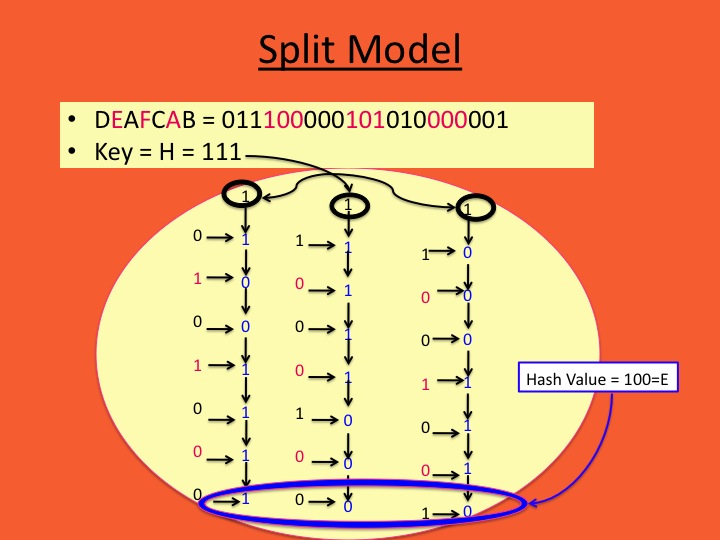
Split Model
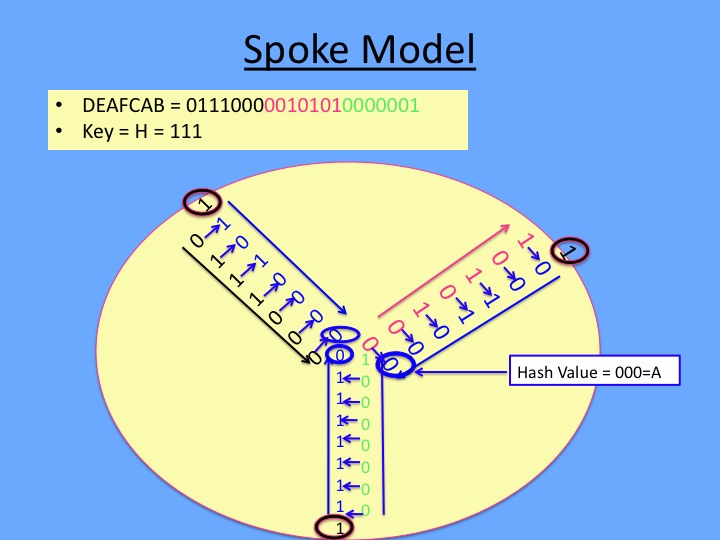
Spoke Model
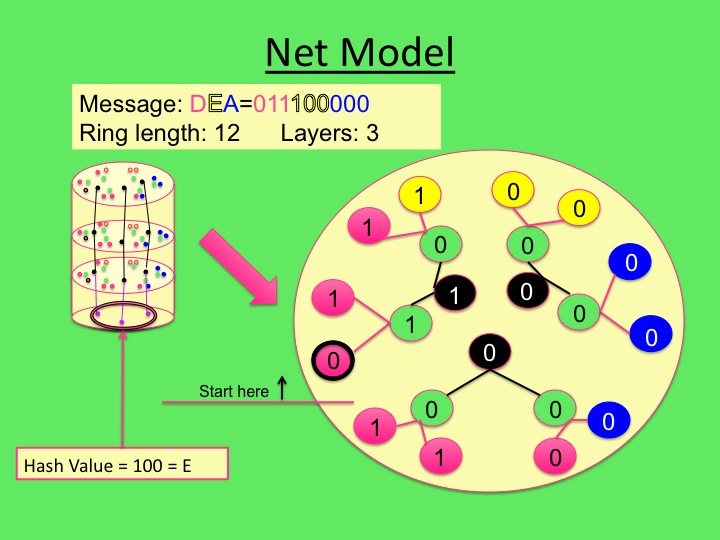
Net Model
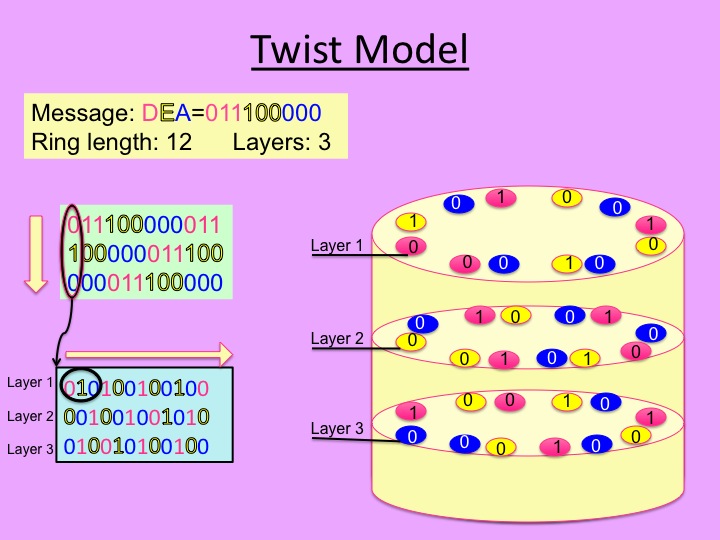
Twist Model
Aaron's Idea
Workin' In, Workin' Out
Matlab M-files for Math Models
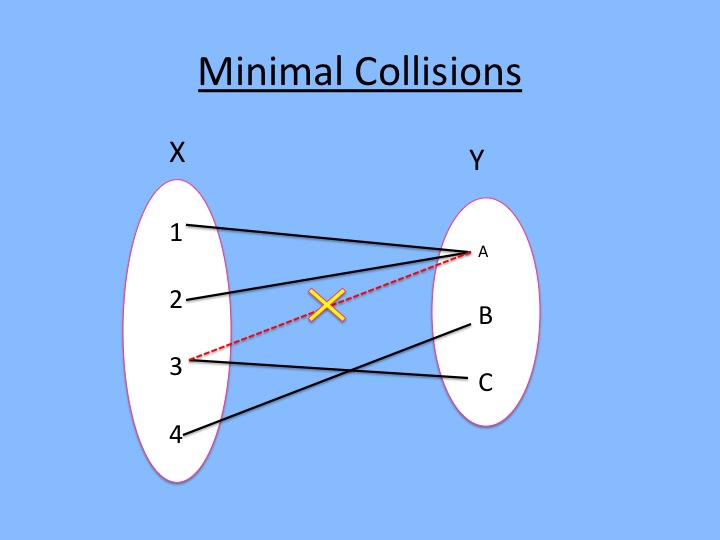
Analysis
Results
Papers
Logical negation
Logical negation is an operation on one logical value, typically the value of a proposition, that produces a value of true if its operand is false and a value of false if its operand is true.
The truth table for NOT p (also written as ~p or ¬p) is as follows:
| p | ¬p |
|---|---|
| F | T |
| T | F |
Logical conjunction
Logical conjunction is an operation on two logical values, typically the values of two propositions, that produces a value of true if and only if both of its operands are true.
The truth table for p AND q (also written as p ∧ q, p & q, or p<math>\cdot</math>q) is as follows:
| p | q | p · q |
|---|---|---|
| T | T | T |
| T | F | F |
| F | T | F |
| F | F | F |
In ordinary language terms, if both p and q are true, then the conjunction p ∧ q is true. For all other assignments of logical values to p and to q the conjunction p ∧ q is false.
It can also be said that if p, then p ∧ q is q, otherwise p ∧ q is p.
Logical disjunction is an operation on two logical values, typically the values of two propositions, that produces a value of false if and only if both of its operands are false.
The truth table for p OR q (also written as p ∨ q, p || q, or p + q) is as follows:
| p | q | p + q |
|---|---|---|
| T | T | T |
| T | F | T |
| F | T | T |
| F | F | F |
Stated in English, if p, then p ∨ q is p, otherwise p ∨ q is q.
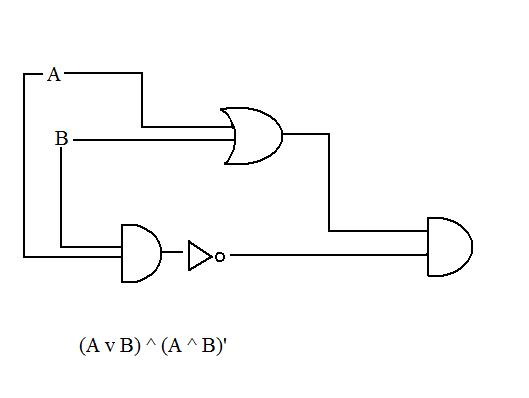
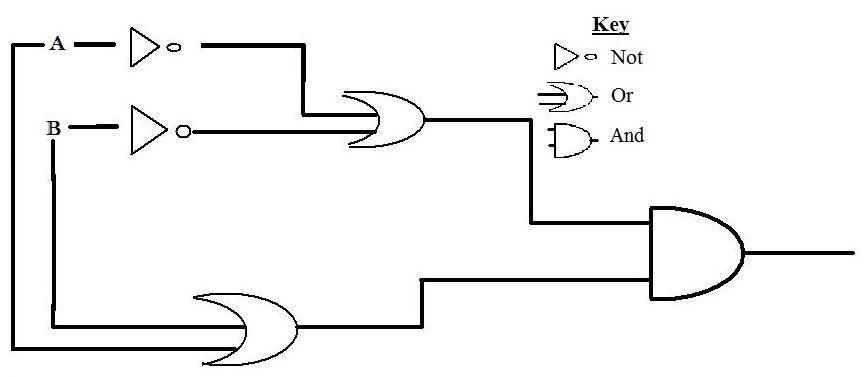
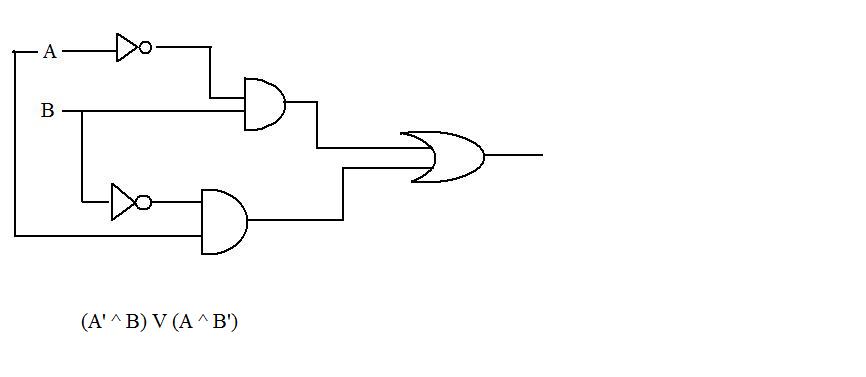
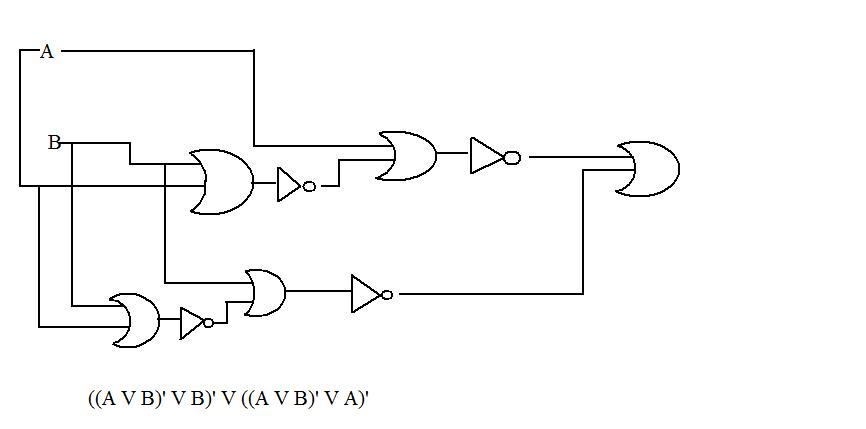
Exclusive disjunction
Exclusive disjunction is an operation on two logical values, typically the values of two propositions, that produces a value of true if and only if one but not both of its operands is true.
The truth table for p XOR q (also written as p + q, p ⊕ q, or p ≠ q) is as follows:
| p | q | p ⊕ q |
|---|---|---|
| T | T | F |
| T | F | T |
| F | T | T |
| F | F | F |
For two propositions, XOR can also be written as (p = 1 ∧ q = 0)∨ (p = 0 ∧ q = 1).
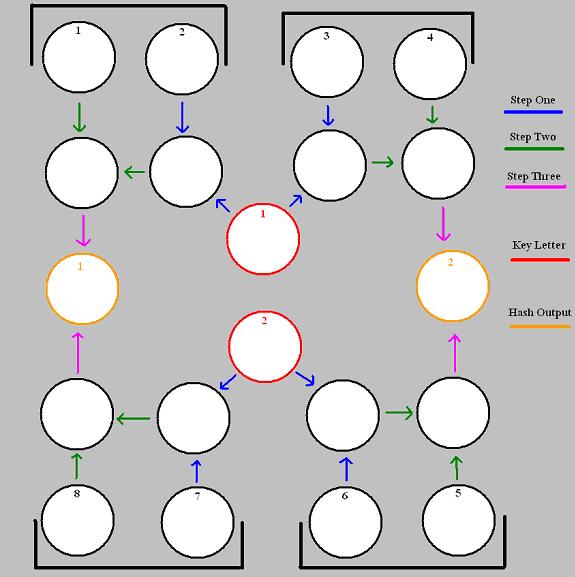
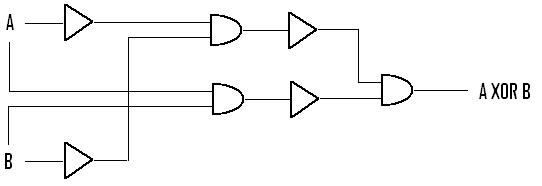
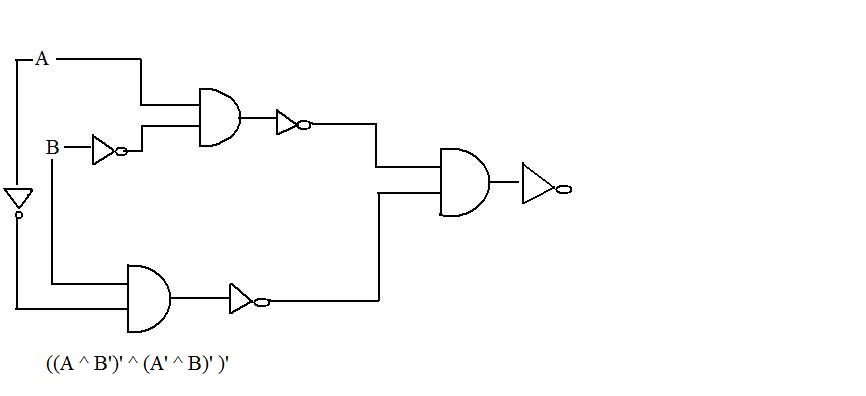
This is the most efficient way of making an XOR with simple opperations.
This diagram is the biological representation to: (A'∨B')∧(A∨B)
The picture above illustrates an XOR gate using only the operations of AND and NOT. While complicated, it appears to be the easiest way to perform an XOR operation with only AND and NOT. There are other ways but seem to involve even more operations. A minimum of 3 ANDs and 4 NOTs appears to be optimal, but is not guaranteed.
Logical NAND
The logical NAND is an operation on two logical values, typically the values of two propositions, that produces a value of false if and only if both of its operands are true. In other words, it produces a value of true if and only if at least one of its operands is false.
The truth table for p NAND q (also written as p | q or p ↑ q) is as follows:
| p | q | p ↑ q |
|---|---|---|
| T | T | F |
| T | F | T |
| F | T | T |
| F | F | T |
Logical NOR
The logical NOR is an operation on two logical values, typically the values of two propositions, that produces a value of true if and only if both of its operands are false. In other words, it produces a value of false if and only if at least one of its operands is true. ↓ is also known as the Peirce arrow after its inventor, Charles Peirce, and is a Sole sufficient operator.
The truth table for p NOR q (also written as p ⊥ q or p ↓ q) is as follows:
| p | q | p ↓ q |
|---|---|---|
| T | T | F |
| T | F | F |
| F | T | F |
| F | F | T |
Stochastic model of E. coli AI-2 quorum signal circuit reveals alternative synthesis pathways Describes a Stochastic Petri Net (SPN) model of AI-2 (Lux), provides XML code and rate constants.
How to break MD5 and other Hash functions.. A paper written by Xiaoyun Wang and her co-authors about how to break MD5 – i.e. how to make collisions occur http://www.infosec.sdu.edu.cn/uploadfile/papers/How%20to%20Break%20MD5%20and%20Other%20Hash%20Functions.pdf Nostradamus attack – i.e. the bit about predicting who will become president by exploiting MD5 http://www.win.tue.nl/hashclash/Nostradamus/
The following was taken from http://www.freesoft.org/CIE/RFC/1321/4.htm
MD5 Algorithm Description We begin by supposing that we have a b-bit message as input, and that we wish to find its message digest. Here b is an arbitrary nonnegative integer; b may be zero, it need not be a multiple of eight, and it may be arbitrarily large. We imagine the bits of the message written down as follows:
m_0 m_1 ... m_{b-1}
The following five steps are performed to compute the message digest of the message.
Step 1. Append Padding Bits The message is "padded" (extended) so that its length (in bits) is congruent to 448, modulo 512. That is, the message is extended so that it is just 64 bits shy of being a multiple of 512 bits long. Padding is always performed, even if the length of the message is already congruent to 448, modulo 512. Padding is performed as follows: a single "1" bit is appended to the message, and then "0" bits are appended so that the length in bits of the padded message becomes congruent to 448, modulo 512. In all, at least one bit and at most 512 bits are appended.
Step 2. Append Length A 64-bit representation of b (the length of the message before the padding bits were added) is appended to the result of the previous step. In the unlikely event that b is greater than 2^64, then only the low-order 64 bits of b are used. (These bits are appended as two 32-bit words and appended low-order word first in accordance with the previous conventions.) At this point the resulting message (after padding with bits and with b) has a length that is an exact multiple of 512 bits. Equivalently, this message has a length that is an exact multiple of 16 (32-bit) words. Let M[0 ... N-1] denote the words of the resulting message, where N is a multiple of 16.
Step 3. Initialize MD Buffer A four-word buffer (A,B,C,D) is used to compute the message digest. Here each of A, B, C, D is a 32-bit register. These registers are initialized to the following values in hexadecimal, low-order bytes first):
word A: 01 23 45 67
word B: 89 ab cd ef
word C: fe dc ba 98
word D: 76 54 32 10
3.4 Step 4. Process Message in 16-Word Blocks We first define four auxiliary functions that each take as input three 32-bit words and produce as output one 32-bit word.
F(X,Y,Z) = XY v not(X) Z
G(X,Y,Z) = XZ v Y not(Z)
H(X,Y,Z) = X xor Y xor Z
I(X,Y,Z) = Y xor (X v not(Z))
In each bit position F acts as a conditional: if X then Y else Z. The function F could have been defined using + instead of v since XY and not(X)Z will never have 1's in the same bit position.) It is interesting to note that if the bits of X, Y, and Z are independent and unbiased, the each bit of F(X,Y,Z) will be independent and unbiased. The functions G, H, and I are similar to the function F, in that they act in "bitwise parallel" to produce their output from the bits of X, Y, and Z, in such a manner that if the corresponding bits of X, Y, and Z are independent and unbiased, then each bit of G(X,Y,Z), H(X,Y,Z), and I(X,Y,Z) will be independent and unbiased. Note that the function H is the bit-wise "xor" or "parity" function of its inputs. This step uses a 64-element table T[1 ... 64] constructed from the sine function. Let T[i] denote the i-th element of the table, which is equal to the integer part of 4294967296 times abs(sin(i)), where i is in radians. The elements of the table are given in the appendix. Do the following:
/* Process each 16-word block. */
For i = 0 to N/16-1 do
/* Copy block i into X. */
For j = 0 to 15 do
Set X[j] to M[i*16+j].
end /* of loop on j */
/* Save A as AA, B as BB, C as CC, and D as DD. */
AA = A
BB = B
CC = C
DD = D
/* Round 1. */
/* Let [abcd k s i] denote the operation
a = b + ((a + F(b,c,d) + X[k] + T[i]) <<< s). */
/* Do the following 16 operations. */
[ABCD 0 7 1] [DABC 1 12 2] [CDAB 2 17 3] [BCDA 3 22 4]
[ABCD 4 7 5] [DABC 5 12 6] [CDAB 6 17 7] [BCDA 7 22 8]
[ABCD 8 7 9] [DABC 9 12 10] [CDAB 10 17 11] [BCDA 11 22 12]
[ABCD 12 7 13] [DABC 13 12 14] [CDAB 14 17 15] [BCDA 15 22 16]
/* Round 2. */
/* Let [abcd k s i] denote the operation
a = b + ((a + G(b,c,d) + X[k] + T[i]) <<< s). */
/* Do the following 16 operations. */
[ABCD 1 5 17] [DABC 6 9 18] [CDAB 11 14 19] [BCDA 0 20 20]
[ABCD 5 5 21] [DABC 10 9 22] [CDAB 15 14 23] [BCDA 4 20 24]
[ABCD 9 5 25] [DABC 14 9 26] [CDAB 3 14 27] [BCDA 8 20 28]
[ABCD 13 5 29] [DABC 2 9 30] [CDAB 7 14 31] [BCDA 12 20 32]
/* Round 3. */
/* Let [abcd k s t] denote the operation
a = b + ((a + H(b,c,d) + X[k] + T[i]) <<< s). */
/* Do the following 16 operations. */
[ABCD 5 4 33] [DABC 8 11 34] [CDAB 11 16 35] [BCDA 14 23 36]
[ABCD 1 4 37] [DABC 4 11 38] [CDAB 7 16 39] [BCDA 10 23 40]
[ABCD 13 4 41] [DABC 0 11 42] [CDAB 3 16 43] [BCDA 6 23 44]
[ABCD 9 4 45] [DABC 12 11 46] [CDAB 15 16 47] [BCDA 2 23 48]
/* Round 4. */
/* Let [abcd k s t] denote the operation
a = b + ((a + I(b,c,d) + X[k] + T[i]) <<< s). */
/* Do the following 16 operations. */
[ABCD 0 6 49] [DABC 7 10 50] [CDAB 14 15 51] [BCDA 5 21 52]
[ABCD 12 6 53] [DABC 3 10 54] [CDAB 10 15 55] [BCDA 1 21 56]
[ABCD 8 6 57] [DABC 15 10 58] [CDAB 6 15 59] [BCDA 13 21 60]
[ABCD 4 6 61] [DABC 11 10 62] [CDAB 2 15 63] [BCDA 9 21 64]
/* Then perform the following additions. (That is increment each
of the four registers by the value it had before this block
was started.) */
A = A + AA
B = B + BB
C = C + CC
D = D + DD
end /* of loop on i */
Step 5. Output The message digest produced as output is A, B, C, D. That is, we begin with the low-order byte of A, and end with the high-order byte of D. This completes the description of MD5. A reference implementation in C is given in the appendix.
Summary The MD5 message-digest algorithm is simple to implement, and provides a "fingerprint" or message digest of a message of arbitrary length. It is conjectured that the difficulty of coming up with two messages having the same message digest is on the order of 2^64 operations, and that the difficulty of coming up with any message having a given message digest is on the order of 2^128 operations. The MD5 algorithm has been carefully scrutinized for weaknesses. It is, however, a relatively new algorithm and further security analysis is of course justified, as is the cas Differences Between MD4 and MD5 The following are the differences between MD4 and MD5: 1. A fourth round has been added. 2. Each step now has a unique additive constant. 3. The function g in round 2 was changed from (XY v XZ v YZ) to (XZ v Y not(Z)) to make g less symmetric. 4. Each step now adds in the result of the previous step. This promotes a faster "avalanche effect". 5. The order in which input words are accessed in rounds 2 and 3 is changed, to make these patterns less like each other. 6. The shift amounts in each round have been approximately optimized, to yield a faster "avalanche effect." The shifts in different rounds are distinct.
Engineering agar
A lab for showing antibiotic resistance across Amp concentration gradient